The security landscape has fundamentally changed. With the often-cited “Zeitenwende,” the pressure to act is mounting dramatically. At the same time, technological, regulatory, and organizational requirements are becoming more stringent.
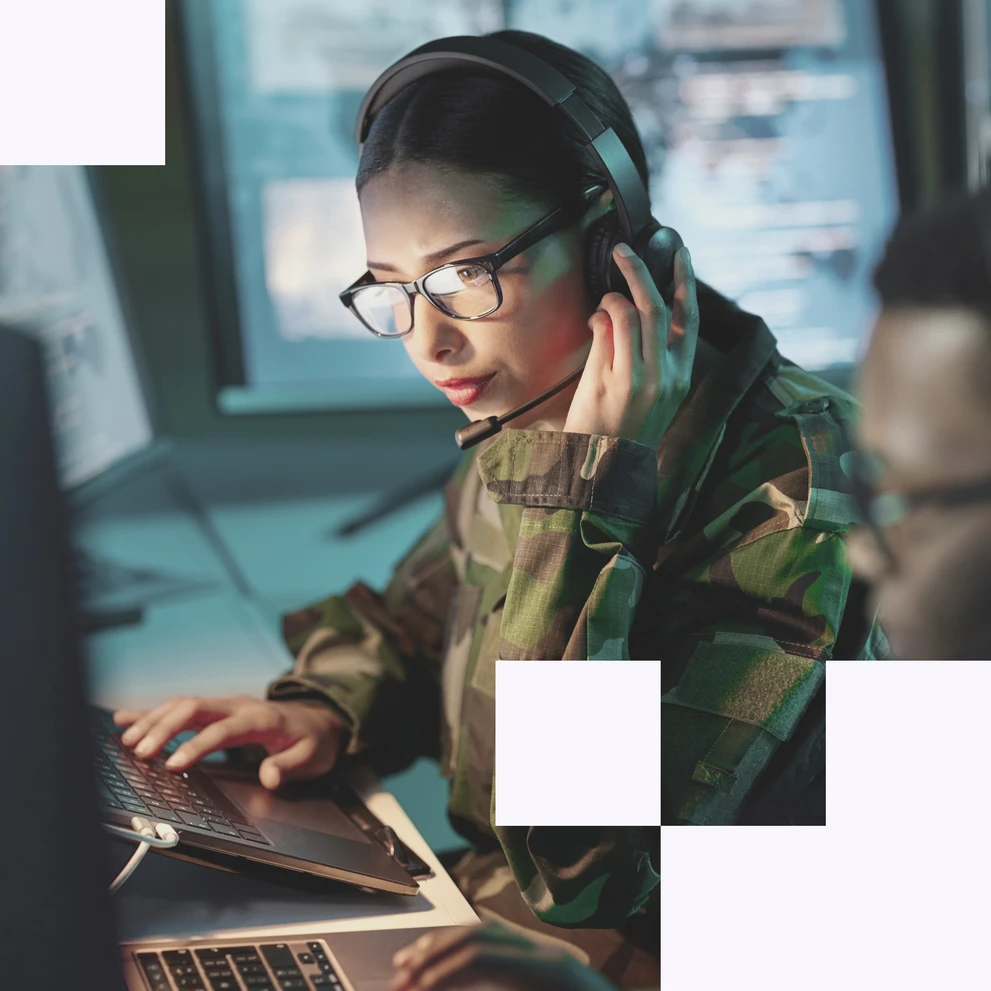
Digital defense does not take place in a protected innovation space. The defense sector must ensure digital capabilities under real-world operational conditions. Under conditions that differ significantly from civilian sectors: Separate domains and networks, high security requirements, strict classification, limited tools, complex verification processes.
Accordingly, digital effectiveness is not determined in the laboratory, but in live operations, under time pressure, in the field. The balancing act between innovation and stability thus becomes an ongoing leadership challenge, and growing complexity increasingly poses an operational risk.